The word cryptography means secret writing. Cryptography is applied to protect data against unauthorized disclosure, better known as eavesdropping. Currently, a very hot topic in this time of ubiquitous communication and cybercrime. Cryptography aims at secrecy of messages by converting messages into apparent nonsense, into a random sequence of characters, which is unintelligible. Cryptography is not the same as steganography. The latter uses intelligible messages to hide a different, meaningful message. An introduction to cryptography can be found here.
The conversion of a message into a cryptogram –not the puzzle in a newspaper– is called encryption or encipherment. The reverse operation is called decryption or decipherment. The use of cryptography implies the use of a secret key. A cryptographic key is an essential amount of information, that has to be kept secret by the owner, receiver of the secret message. Depending on the cryptographic system used: symmetric or asymmetric, the sender uses the same secret key, or uses a public key that corresponds to the secret key, but does not reveal the secret key. In the asymmetric case, certificates of authenticity and validity are required, giving rise to networks of certification and registration authorities. In any case the management of cryptographic keys is a very important part of cryptographic systems in practice.
In many different projects and product developments with Philips, SafeNet, Banksys, DeltaCrypto and Compumatica in the roles of cryptographer, security architect and senior consultant, I exercised the more practical aspects of cryptography.  Much of the R&D involved designing of cryptographic algorithms (mathematics), management systems and method for cryptographic keys, random number generators, integrated circuit electronics (chips) and –often embedded– application software. Many of the security appliances designed were intended for the highest degree of security, national security of state secrets. High grade, high security and high assurance. The picture left shows me in September 2004, operating a UP6317 Secure Telephone from Philips Crypto B.V. A magnificent collection of cryptographic devices with extensive and detailed descriptions can be found at the online Crypto Museum.
Much of the R&D involved designing of cryptographic algorithms (mathematics), management systems and method for cryptographic keys, random number generators, integrated circuit electronics (chips) and –often embedded– application software. Many of the security appliances designed were intended for the highest degree of security, national security of state secrets. High grade, high security and high assurance. The picture left shows me in September 2004, operating a UP6317 Secure Telephone from Philips Crypto B.V. A magnificent collection of cryptographic devices with extensive and detailed descriptions can be found at the online Crypto Museum.
There was, however, an other side to the “crypto coin”… Cryptographic applications, appliances and software were considered startegic goods. Therefore, these security goods could not freely be exported to all countries. In order to realise sales abroad, which was a must for a commercially operating company like Philips, the strength of the cryptography had to be reduced. Contrary to everything written and otherwise communicated, this degradation of cryptography was realised in consultation and collaboration with government services and agencies in those days, the former NLNCSA (Netherlands National Communications Security Agency). The security weakening was implemented in various and often resourceful and innovative ways in cryptographic algorithms and random number generators. An example of such a weakening is the PX-1000 pocket telex, extensively descibed at the site of the Crypto Museum.
And indeed, this was a serious weakening directed by the NSA, the US National Security Agency. The Dutch radio program Argos on Saturday 20th April 2019 revealed how the NSA changed the algorithm of the PX-1000 pocket telex, a consumer encryption device, with help from multinational electronics giant Philips. An exciting story dating back to 1984.
The Aroflex Cryptography
Aroflex is the name of the cryptographically secured Siemens T-1000 teleprinter by Philips Usfa B.V. Please, see this Aroflex page at the website of the Crypto Museum. It contains a large amount of details about the machine, its history and role within NATO.
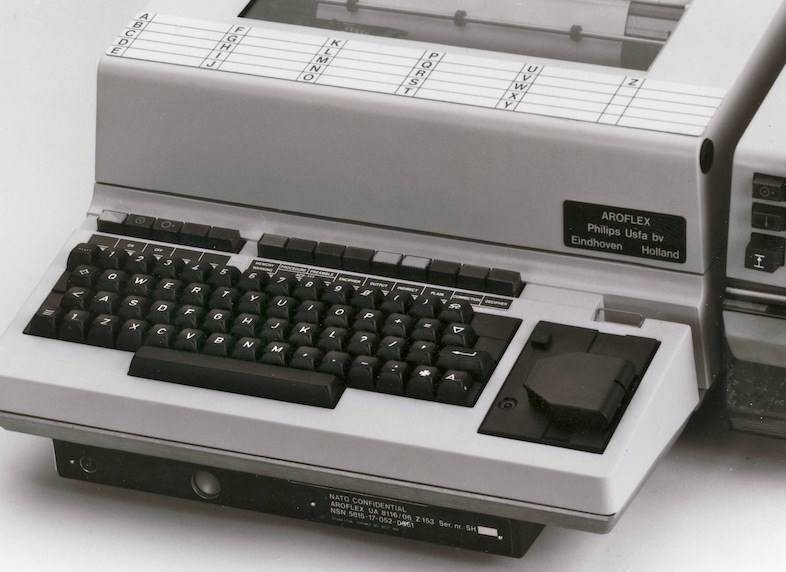
Aroflex came in two basic types, one type, denoted by the name Aroflex, intended for use by NATO and allies in NATO countries. The other type was simply named T-1000 CA, and was intended for applications in the non-NATO part of the world. Aroflex machines were sold exclusively by Philips Usfa, whereas the T-1000CA machines were initially sold by Siemens only, but later on also by Philips Usfa.
Two Crypto’s
As can be read on the website of the Crypto Museum, the cryptography used by the two types are quite different, even in the hardware electronics used, i.e. the use of two different integrated circuits OQ4406 and OQ4407. The latter was derived from its predecessor 4406 by a relatively simple mask modification, which effectively erased part of the circuit. This modification was also a very low cost operation.
The technics
The cryptographic algorithm of the T-1000CA was commonly referred to as the Beroflex algorithm. Each machine type would be available in many cryptographic variants. These variants were mainly based on values of fixed bits in the daily key and message key settings, and the number of initialization cycles. Both algorithms comprise eight sections, which used to be called ‘wheels’ in the old days, with so called shift registers and Boolean circuitry. Each section can store sixteen key bits and implements a shift register of length five. Hence, the secret key that can be stored has a total length of 128 bits. One kind of Aroflex variants has the possibility to set, at production time, the order in which the 8 sections influence each other. An example of a machine with this order permutation is the UA8116/04, also known as ‘Politieflex’. The cryptogram produced by the telex encryption devices is neatly formatted in lines with at most 10 five letter groups and has a cryptographic preamble, aka message key, of 10 five letter groups. The first five groups show a five times repeated single five letter group, containing 25 random bits. These 25 bits are used together with 31 fixed bits to initialize the registers in the cryptographic algorithm in the so called alfa-mode. The second part of the message key consists of a five times repeated five letter group, encrypted with the daily key. Because of this encryption, this second part cannot (easily) be distinguished from the cipher text itself, at least not with Aroflex… With the exception of one variant, Beroflex machines exhibit a statistical bias in the second part of the message key. This is a useful property to inform the cryptanalyst about the machine type that produced the cryptogram! Besides, encryption of redundant text (the 5 times repeated five letter group) is a bad idea in cryptography, as it provides the cryptanalyst with a means to check the correctness of the guessed key bits or other parameters.
Strong and weak
The cryptographic strengths of both machine types differ by magnitudes! The Aroflex uses a 96 bit cryptographic key (the daily key), derived from 24 telex alphabet characters a…z. In addition it has 32 fixed key bits, which are stored in two sections. These fixed key bits are optionally customer unique. Assuming absence of any exploitable weaknesses, the cryptanalyst would have to launch an exhaustive key search of 2^96 (79,228,162,514,264,337,593,543,950,336 combinations), totally out of reach for any computer or special purpose hardware in those days. Beroflex uses only 90 bits of the 24 character daily key, and additionally 38 fixed key bits: two sections and one bit in the remaining six sections. A major difference, however, is that the internal state of the Beroflex algorithm is independent of the daily key setting, whereas the Aroflex internal state does depend on the 96 key bits! To get some dependency on daily key bits, Beroflex has a special mixing mode, called beta-mode. However, this mode makes use of only 24 generated key stream bits. Consequently, this is the only unknown parameter the cryptanalyst has to find out by exhaustively trying all 2^24 (= 16,777,216) combinations and check the second part of the message preamble for equality of the five groups of five characters. One has to solve a linear set of equations for at most 16.7 million combinations to find this solution. Way back in 1980, this was a task that would take considerable time on existing computers. Therefore, a special chip and hardware was designed for the agencies to speed up these calculations and facilitate the decipherment of any T-1000CA encrypted text.
Business and backdoor
The Aroflex machines could only be sold to NATO partners and friendly allies. The T-1000CA was sold to many countries , governments, police forces and companies around the globe, thereby giving agencies access to a huge amount of sensitive ‘encrypted’ information, exchanged over the world wide telex network. Also, it enabled companies like Philips Usfa and Siemens to realize more sales and so compensate the considerable investments in the development of the machines. It remains, however, hard to imagine that the Dutch agencies did not have any active involvement in the development of Beroflex. B after A, a relatively sophisticated weakening of a high grade, NATO approved cryptographic algorithm. No commercial company would go through such an effort itself, with the risk of being exposed, resulting in total loss of trust and deprived from further sales.
The Chinaflex Adventure
Afairs that take place in 1986-1987 at Philips Usfa B.V., Meerenakkerweg 1, Eindhoven and in Hong Kong. An enthusiastic junior salesman from that company has taken up a plan to sell Aroflex machines to China… A story written down in November 2000 and edited in January 2020
Once upon a time…
In those days three employees with identical names were working with Philips Usfa, their initials being ‘AB’. One was a security officer, who had an extra letter ‘t’ in his name, and one was HR manager. The youngest of the three was a salesman. He and his colleagues from the sales department had challenging tasks to sell cryptographic equipment in national and international markets. Challenging, as strict rules and export laws with respect to the sales and export of strategic goods applied in those days. Quite coincidentally I discovered that junior AB had a nickname ‘Pico B’ in certain government circles. It was never made clear to me how AB got this nickname, but besides being the youngest AB, he was also quite inexperienced with cryptographic appliances, in particular what kind of equipment one was allowed to sell to customers in the various countries around the world. Maybe, his name had something to do with the Picoflex crypto device. Picoflex can be seen as a small version of Aroflex, being interoperable with the latter equipment.
Pico B was very motivated to score career points and imagined, not bothered by relevant knowledge of cryptography, that he could sell Aroflex equipment in the Far East. He also liked travelling very much and told me once that he had a free airline ticket (from KLM’s Flying Dutchman frequent flyer program) every now and then, which he used to take his wife on an intercontinental flight.
At the time, an agreement was in place between Siemens, the producer of the T-1000 telex machine, and Philips Usfa, who designed and manufactured the crypto unit underneath the telex machine. That agreement implied that Philips could serve the national and NATO markets, and a few other friendly countries with the high grade Aroflex . Siemens, however, could serve the remaining part of the world, not with Aroflex, but with the cryptographically much weaker lookalike T-1000CA. The Aroflex device was approved by SECAN, the NATO institution that tests all cryptographic equipment for suitability and use within NATO. Aroflex complied with the highest requirements for cryptographic security and Tempest (spurious radiation and black line conduction of information). The T-1000CA , CA from Crypto Appliance, was known to insiders as Beroflex. Note the A-B here. Other special Aroflex and Beroflex versions were manufactured as well. These telex machines were identified with other letters such as T-1000CB and T-1000CZ. The machines are generally identified by their type numbers. The NATO Aroflex has type number UA 8116/02, and there also exist UA 8116/04, /05, /50, /51, /09, /10, see also the list on the website of the Cryptomuseum.com. Most likely, the success of the Aroflex was a motive for the marketing and sales department of Philips Usfa to go the opposite way and launch ‘commercial’ Aroflex machines on the market.
On the way to Hong Kong
One day, Pico went on his way to Hong Kong to meet a large delegation of Hong Kong Chinese and present a comprehensive product portfolio of Aroflex. He was sure that an enormously large order was ‘in the air’. Once he had arrived there, the largest part of the audience turned out to be people from the Peoples Republic of China. These Chinese visitors were up to the one and only real Aroflex, the one used by NATO, as later would become clear to Pico. The Chinese were seriously interested, and they even mentioned an initial purchase of 2000 machines. The catalogues of those days listed prices of more than 20,000 Dutch Guilders per machine, and such a large order would mean several times the annual turnover of Philips Usfa, and obviously a rise in position and salary for Pico. The follow-up meeting was planned and would involve a demonstration on the spot of Aroflex machines.
Sometime later Pico leaves for Hong Kong again, this time accompanied by a colleague from Usfa, who knows the operation and the service of the machine very well. The two guys plan to demonstrate the machines hands-on and to give an introductory instruction course. Two Aroflex telex machines are shipped. Clearly, these Aroflex machines are not the real UA 8116 Aroflex versions, this is ruled out by the export laws and regulations. These machines are T-1000CA’s with a customer unique cryptographic variant, that I have devised. This is something I do more often, nothing special, because in this way one creates a complete separation of user groups. After all, even with the correct secret key of one group, somebody from another group can still not decrypt messages, or inject false messages in the network of the group.
The room was filled even redder than at the first visit!
Pico panics
Shortly after the start of the course, voices from the audience sound. They don’t need such a course, they already know how to operate and service these machines. They want the cryptographic algorithm, the mathematics explained! Alas, that is too difficult a question for Pico and his colleague. The communist Chinese become a little irritated and some of them walk towards the Aroflex machine, prepared for the demo. They start ‘playing’ with the machine, typing in and printing something. Next, they walk out of the demo room to a nearby telephone and a conversation arises which is unintelligible to the Dutch guys. The Chinese conversation ends with disapproving looks in the direction of the so called Aroflex machine. “This is no Aroflex”, they tell the Usfa men! Imagine the faces of the two… What do the Chines mean? Pico has consulted me and I promised him a ‘real’ Aroflex, didn’t I? Everyone is angry, the Chinese people, Pico and colleague, the Hong Kong Philips agent. It looks as if the whole exercise is useless, a fake. The Philips agent even threatens with a claim.
I was called on the phone by a nervous Pico, who explained me that a different version of the crypto telex must become available for the Chinese, something much more like Aroflex… Not sure if he was understanding the situation, I answered that he was asking for the impossible. I explained him that I could come up with a version of more or less equal strength that differed from the T-1000CA they had demonstrated over there in Hong Kong. Asking me how long that would take me, I gave him an estimate of six weeks. It was decided to go that way and Pico was a little more reassured, was able to calm down the Chinese people, and return to Eindhoven safe and sound. The six week estimate turned out to be a little optimistic, as it would take more than four months for prototypes of the modified electronic crypto unit, comprising an altered algorithm, and accompanying embedded software, to become available. My estimates usually were slightly optimistic, for the paperwork and other project issues used to take a lot of time in those days.
The big question, of course, was how the Chinese people were able to find out that the Aroflex machine demonstrated was not a real, not a NATO version, Aroflex?
The mystery solved
The type plate of the crypto unit underneath the telex machine shows its type number. This type number should correspond one-to-one with the cryptographic version of the machine. For example UA 8116/02 indicates that the cryptography is of the NATO version. However, type plates can easily be replaced… There are three properties exhibited by machines from the Aroflex /T-1000 family, that are typical for the built-in cryptographic versions of the machines.
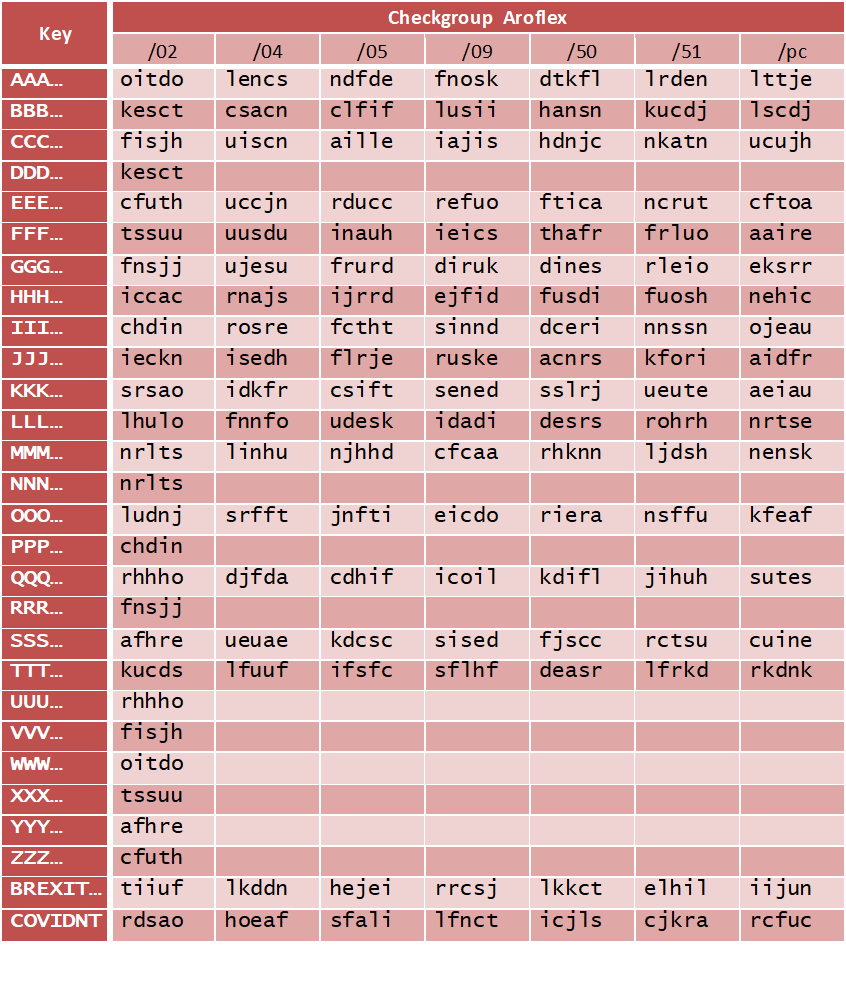
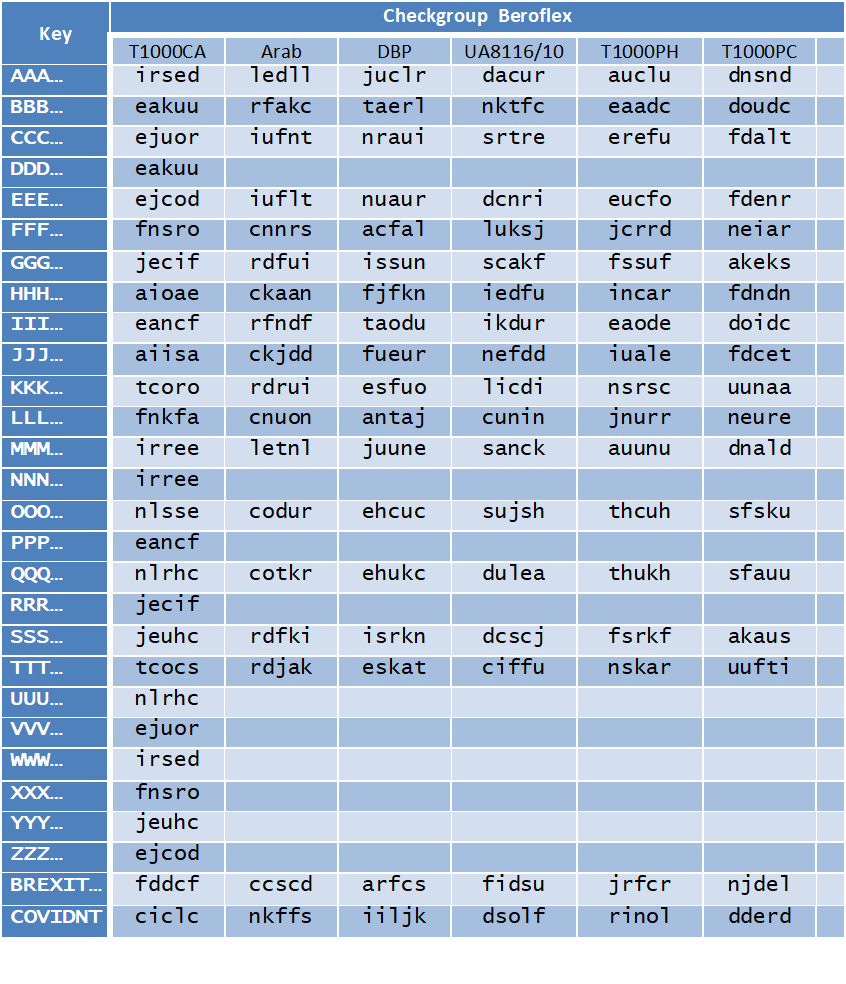
- The key checkgroup
If an Aroflex or T-1000CA is loaded with a cryptographic key , either by typing in 24 characters on the keyboard, or by feeding in an punched paper tape, then the machine will print a check group of five letters. This check group depends on the key loaded and is calculated by the crypto unit, and, consequently depends on the cryptographic version of the machine. The check group is a so called one-way function of the key. An Aroflex / T-1000CA cryptographic key consists of 24 letters from the telex alphabet a to z. The 4 least significant bits from the letter code according to the international alphabet CCITT-2 (ITA-2) are used as keybits, producing a cryptographic key of 24×4 = 96 bits. Similarly, the check group of 5 letters corresponds to 20 bits. For example, a key of 24 times the letter ‘b’ results in a check group ‘kesct’ with a UA8116/02, but ‘csacn’ with a UA8116/04, and ‘clfif’ with a UA8116/05. A standard T-1000CA machine will print ‘akuut’ for that key. Besides, the key with 24 times the letter ‘d’ results in the same 96 keybits as the ‘b’-key, and therefore the same check groups. Once you have played with an Aroflex on some show or exhibition, you have a number of key-check group combinations in your hands. Interesting to know: check groups calculated by T-1000CA machines are linear combinations of keybits, which is helpful for the cryptanalyst in finding the secret key.
- A shorter T1000CA key
Maybe a little harder to find out is the fact that T1000CA machines use shortened cryptographic keys of only 90 bits. In fact six keybits are replaced with constant value bits, which means that clusters of 64 keys exist, resulting in identical encryption. If the Chinese had somehow gotten hold of a T-1000CA machine, they would probably have found out about this feature.
- Statistical deviation in the second part of the message key
An Aroflex cryptogram consists of several different parts. First, a five letter group, the GSI, not relevant in this context. Next, a five times repeated five letter group, forming the first part of the message key, i.e. a randomly generated string of 20 bits. Thereafter, five groups of five letters, forming the second part of the message key repeated five times and encrypted with the first part of the message key and the selected cryptographic key. In Aroflex documents the latter key is commonly referred to as daily key. After the message key preamble, the cryptogram starts formatted in five letter groups. Encryption of the message is performed with a modified daily key, the modification being a cryptographic procedure on the original daily key with the total message key.
The encrypted second part of the message key does not have a uniform statistical distribution, and this becomes evident with testing. Explaining the details of this phenomenon involves a cryptographic and technical explanation that I omit here. It is not unlikely that the Chinese were informed of this property, or had discovered it themselves.
Chinaflex appears
A simple modification of the T-1000CA apparently as not sufficient to satisfy the Chinese. In order to achieve that, the three properties mentioned before had to be taken care of. To me it was clear that a software-only modification would not be sufficient. After all, the machine’s software resides in (old 1 Kbyte) EPROMS –semiconductor memories– that are not protected against unauthorized reading. Some modification had to be performed on the hardware crypto unit. So I turned to my colleague Herman K, a very skilled electronics designer. Herman had mastered higher electronics from Philips courses, coming from high school. Consultation with Herman resulted in a few minor changes that could be done manually. The fact that crypto units were always potted for physical security, and integrity of the unit’s operation, allowed us to add some extra wires and a little extra integrated circuit. Herman placed this extra component on top of some existing circuitry, so that it would be hard to recognize if Roentgen photography would be applied to the unit. Finally, prototypes of the crypto unit arrived and were baptized Chinaflex modules. This descendant of the T-1000CA family received an official name and type plate with UA number.
The entire circus of presentations and demonstration in Hong Kong was redone quite some time later. The same ritual: a couple of Chinese guys hit the keyboard of the Aroflex machine, ran to the telephone, got in touch with their home base, and… were completely satisfied! The Chinese embassy in the Netherlands contacted the management of Philips Usfa. One day, the Chinese flag was waving in front of the main building at the Meerenakkerweg in Eindhoven. A delegation from China was welcomed and talked with CE, the head of the marketing and sales department at the time. Philips was promised a great future in China with the Aroflex; a first purchase of 2000 machines was mentioned. Of course the were some conditions, such as assembly and production in China. Furthermore and very important, before a first order could be placed, Philips Usfa had to fully disclose the cryptographic algorithm, which subsequently had to be analysed and approved by Chinese cryptographers.
End of exercise
No surprise that the party was cancelled. Philips could not and did not agree with the conditions of the Chinese. No order was ever placed. No more than a few prototypes were made. Studying the Aroflex check group mechanism led to a paper at the 1986 Benelux Symposium on Information and Communication Theory entitled “Key Signature Schemes”.
Recent research in old archives reveals an interesting fact about Chinaflex and the T1000PH.
The final Chinaflex version developed by NSA
A document of US origin dating back to October 1986 was retrieved from an old archive showing the involvement of US intelligence agencies in the development of the final Aroflex version for China. This Aroflex version was called T1000PH, PH for Philips Hong Kong. In my personal notes of a meeting between Philips Usfa management and officials of the Netherlands National Communications Security Agency NLNCSA (NBV), I noted in a short sentence that the then interim director of the NLNCSA was not pleased with that name.
It was October 1986, the same year the Turkish Aroflex version, developed by Philips Usfa B.V. from Eindhoven, The Netherlands with the involvement of the US National Security Agency, was delivered in quantities to the Ministry of Foreign Affairs of Turkey. Although the chances of sales to China were estimated as very small by the Americans, they considered this opportunity of strategic importance and developed a low security cryptographic version based on the T1000CA. The same hardware crypto unit, but with embedded software that does not have the shortcomings of the standard T1000CA. Just like with the Turkish Aroflex, all 96 keybits are used, and loaded into the cryptographic hardware in a different order. Also the second part of the message key is additionally ‘encrypted’ by modulo 26 addition of 25 encrypted ‘z’ characters. These 25 ‘z’ characters are encrypted by using the first part of the message key only. Instead of the secret daily key, a threefold repetition of the message key including fixed unique bits is used. This extra encryption results in roughly one million (220 ) possibly different encryption strings of 25 telex letters to disguise the second part of the message key, thereby effectively removing the bias in this part of the message key. It should be noted that the method outlined here is not identical to the method implemented in the Turkish Aroflex. This obviously makes sense, since no one wanted the Chinese –well known for their reverse engineering capabilities– to find out about the Turkish Aroflex affair.
The modifications in the T1000CA machine
The embedded software of the T1000CA is stored in eight EPROMs (Erasable Programmable Read Only Memory) as shown in the picture of the Aroflex crypto unit. Number 1 is at the top right of the picture, and number 8 at the bottom right. These EPROM’s are of the type AM2708DC with a capacity to store 1024 bytes. Hence, the total size of the embedded software does not exceed 8 kilobytes. The modifications for the T1000PH are in EPROMs 3,5,7 and 8, one EPROM more than for the UA8116/10 for Turkey.

Aroflex and Beroflex Key Check Groups
The tables below list a number of cryptographic keys and the corresponding key check groups for all different versions of Aroflex and Beroflex. The bottom two last keys in the list are respectively : BREXITINTWENTYTWENTYDONE en COVIDNTPANDEMICKILLSMANY

 Cryptography has grown into a science. Courses highlighting the different areas of cryptography are given at many universities around the globe. I have been in the privileged position to contribute to the broad area of cryptography by means of courses, lectures, the establishment of a master degree in the security of information technology at the Eindhoven University of Technology (TU/e) in the Netherlands. Also by research contributions with colleagues from Bergen University (UiB) in Norway. Many of my publications can be found
Cryptography has grown into a science. Courses highlighting the different areas of cryptography are given at many universities around the globe. I have been in the privileged position to contribute to the broad area of cryptography by means of courses, lectures, the establishment of a master degree in the security of information technology at the Eindhoven University of Technology (TU/e) in the Netherlands. Also by research contributions with colleagues from Bergen University (UiB) in Norway. Many of my publications can be found